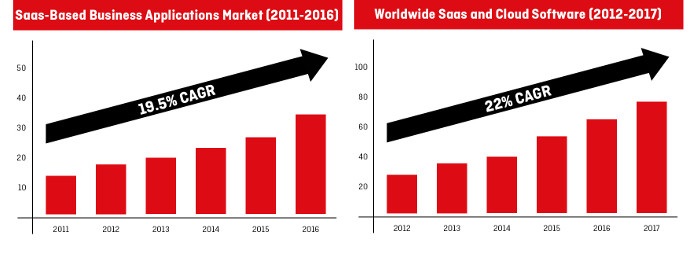
Cloud adoption in the enterprise environment is on the rise. A recent study from Centaur Partners states that revenue generated from SaaS and cloud-based business-application services will increase from $13.5 billion in 2011 to $32.8 billion in 2016 (a CAGR of 19.5%).
The need to adopt SaaS within the enterprise environment is becoming stronger as the increase in benefits grows.
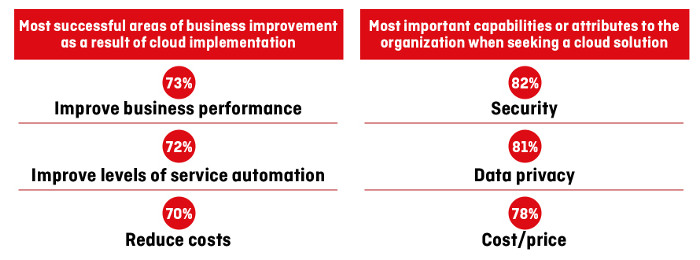
Some of the main benefits of cloud adoption were highlighted in the findings from the 2014 KPMG Cloud Survey, which revealed that the top three improvements businesses noticed since the implementation of cloud included improved business performance, improved levels of service automation, and reduced costs.
For enterprises, however, switching from on-premises software to SaaS carries with it some big concerns, including security and data privacy.
On-premises software allows companies to store sensitive information and data on their own infrastructure, which helps keep it secure and protected. In the case of SaaS, the onus of keeping user data safe falls on the software provider; therefore, it is not surprising to see that security and data privacy are the top two capabilities organizations are looking for in cloud solutions.
While on-premises software will ultimately provide enterprises with more control over their data, there are a number of features software vendors can include in their SaaS apps and platforms to address these concerns.
Features for Enterprise-Grade Software
It is clear that the features included in enterprise-grade SaaS should revolve around addressing business concerns, solving business problems, and ensuring the software is able to provide the availability and efficiency needed in the ever-challenging enterprise environment.
With that being said, here are five features software vendors should include in their enterprise-grade SaaS applications and platforms.
1. Security and Data Protection
With every new case of a company getting hacked, the need for security increases.
The security issue is one that challenges companies on a daily basis, mostly due to challenges in surveilling who is accessing what and when, and the sheer number of ways a company can get hacked.
Therefore, when building enterprise-grade SaaS, there are many different security factors companies need to take into account. Most security aspects are connected with the actual development and the quality of the software’s code, but some are features that can be built and implemented quite easily. The two main features include:
User Privileges
Today’s hackers are not just the ones wearing Guy Fawkes masks – they can even be disgruntled employees who want to take revenge on the company, and if the disgruntled employee has access to the company’s system, it is much easier for them to steal sensitive data than it would be for an outside attacker.
The user-privileges factor is two-sided:
First, you should grant users with as little permission as possible and be very strict on the permissions you grant. This will help you prevent users from accessing things they don’t need to access, and quickly identify who had access in the event of unauthorized activity so you can take quick action and resolve the issue before it gets out of hand.
Second, you should create multiple privileges for each user. Let’s say you want to determine a set of permissions for admin accounts. You may have multiple admin users and not all of them will require the same privileges.
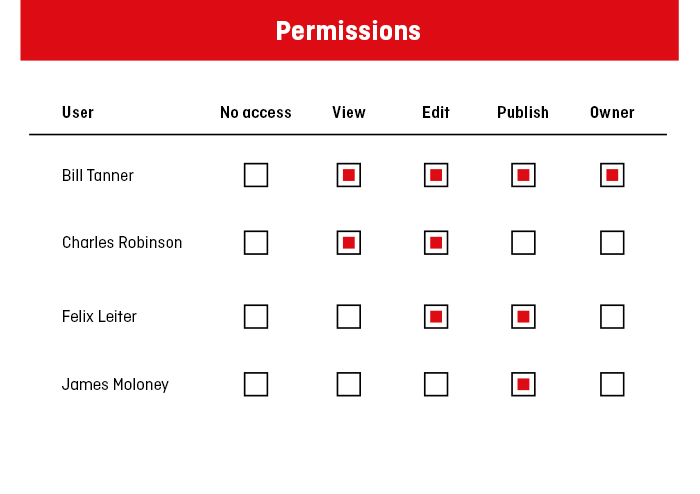
So, for example, you may grant one user an admin role to create, edit, and update user accounts, and grant another user an admin role to create, manage, and assign groups. This will add another layer of security to your already-tight user privileges.
Strict Login Policies
When it comes to gaining unauthorized access to a user’s account, hackers use a number of techniques, such as phishing, keylogging, and trojan horses. While most types of attacks can be prevented by using anti-virus software or implementing strong security measures within an organization, one common entry point for hackers is via the login screen.
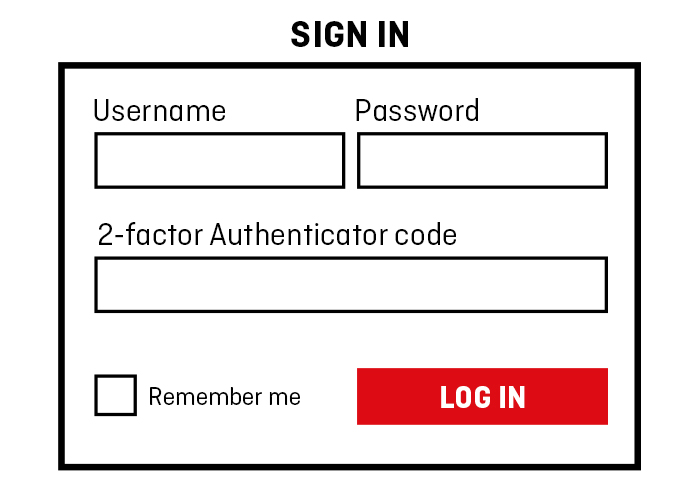
Gaining unauthorized access to a user’s account via the login screen is not as difficult as one would imagine, especially when you consider that the most common passwords are ones like password, 123456, and qwerty. These types of simple passwords are low-hanging fruit for hackers and make the security of a piece of software severely vulnerable.
And part from the example mentioned above, there are a few other techniques hackers use to gain access to someone’s account.
Therefore, when building the login feature for an application or a platform, it’s paramount to include a number of different security features (such as a two-factor authentication) to increase the security at the login level.
2. Privacy
Privacy within the SaaS world is a red-hot issue, especially for enterprises, as keeping their users’ privacy safe and protected according to privacy-compliant regulations is one of their main priorities.
Ever since Edward Snowden blew the whistle on U.S surveillance programs, the online privacy issue has been front and center and has led to foreign governments changing regulations – the recent invalidation of the Safe Harbor pact is a prime example.
Therefore, it’s paramount that the software not only be secure, but also adhere to privacy regulations and best practises.
3. Customization, White Labelling, and Extensibility
Out-of-the-box solutions tend to provide consumers with all the features and functionalities they need, and if they don’t, there is usually a premium option available to provide these missing parts.
For enterprises, however, getting the right features that solve business problems or enhance workflows is often hard to achieve with standard out-of-the-box solutions, which is why the need to customize and extend the software is so great.
Customization
Customization is not really a feature, but rather a service (i.e. custom SaaS development). For enterprises, however, customization often provides an essential competitive advantage. For this reason, it’s vital that the software and architecture be built with future customization in mind.
White Labelling
Building enterprise-grade SaaS is not only about providing companies with quality software, but also offering other businesses the opportunity to sell it to their customers, which requires white labeling. The ability to white label your software involves building it in a way that will allow other businesses to change the colour scheme, replace logos and corporate branding, and remove or replace company references in the code.
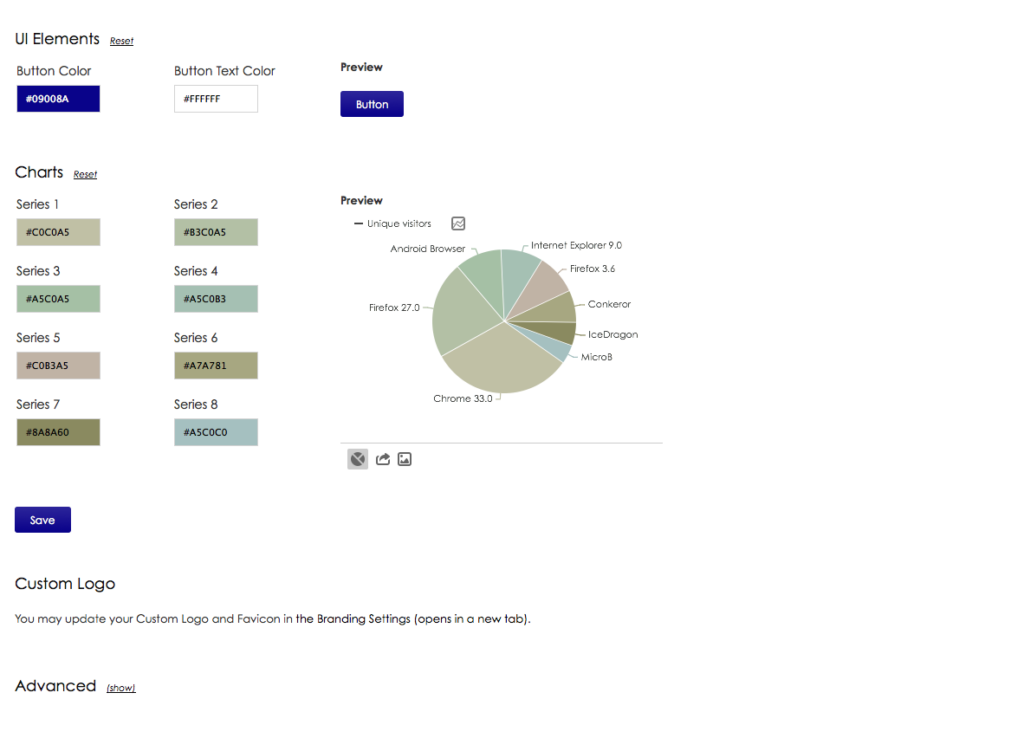
The white labelling feature can either be built-in, or developed as a plugin and offered to clients as a paid feature.
Extensibility
The software also needs to built with extensibility (e.g. with plugins) and the future in mind in order to provide users with software that can be enhanced to meet ever-changing needs and requirements.
As previously mentioned, providing extensibility options can often be included as part of a premium service or as another revenue stream.
4. Integration and Compatibility With Other Systems
A recent survey conducted by THINKstrategies and MuleSoft found almost 90% of SaaS and cloud providers stated integration is important to winning customer deals.
Today’s enterprises utilize a number of systems and software, and using new software that integrates with existing solutions is becoming more and more essential.
By building software that can be easily integrated into their main systems, such as SharePoint and SalesForce, companies can centralize their tools and reduce the disruption to their end users.
5. Scalability and High performance.
Enterprises are designed to scale, and their software should be, too.
Building high-performance, scalable software comprises of many different aspects – the software’s architecture, the infrastructure setup, and the quality of the code, just to name a few.
While there are a number of ways to tackle the scalability and high-performance issues, there are a few key areas to consider:
Multitenancy
Multitenancy is when a piece of software runs on a server, but provides that software to many companies (aka tenants). Apart from providing the software vendor with a range of cost savings, multitenancy also allows the software to scale more easily (compared to single tenancy).
Content Delivery Networks (CDN)
A content-delivery network is a series of servers located in different parts of the world that caches content and delivers it to users closer to their location.

For example, if your web server is located in the U.S., but a user from Germany wants to access your software, your web server will send the content to a node located either somewhere in Germany or somewhere close by and then display it to the user, increasing load time, providing high availability, and delivering better performance.
Redundancy and Disaster Recovery
Redundancy in SaaS refers to the duplication of key components and backing up data to prevent data loss in the event of a failure.
Disaster recovery involves putting a plan in place (a Disaster Recovery Plan – DRP) that will protect the organization in the event of a catastrophic human or natural event. Disaster recovery is a subset of business continuity.
Ensuring that both these points are addressed when building enterprise-grade SaaS will protect companies from sudden data loss and will maximize uptime.
It’s Not Just About the Features
The first step in building enterprise-grade SaaS is to start with the features mentioned above, but the requirements go much deeper than that. It’s a combination of solving business challenges and providing companies with the support they need to tackle the constantly competitive enterprise environment.